Disposable quick tunnels
Best for trying Cruma fast or sharing a localhost app for a short test.
- ·3-hour session limit
- ·Heavily rate-limited
- ×No custom domains
- ×No end-to-end encryption
Cruma gives anything running on your machine a public HTTPS URL — from a quick CLI tunnel to a full desktop app with request inspection. Free for personal dev, with paid tiers for custom domains, end-to-end encryption, and built in authentication.
$ cruma proxy http localhost:3000https://random-id.tun.cruma.io
LIVE
$ cruma serve ~/example-wwwhttps://random-id.tun.cruma.io
LIVE
Anonymous tunnels are heavily rate-limited, not end-to-end encrypted, and end after 3 hours. Free registered tunnels remove the time cap but still don't support CNAMEs or E2E. Free is for individual, non-commercial dev use — paid plans unlock the full feature set.
Free tunnels for quick testing, paid tunnels for custom domains, stronger privacy, and consistent performance. Free is for individual, non-commercial development use — not company-wide rollout.
Best for trying Cruma fast or sharing a localhost app for a short test.
Repeat use, moderate bandwidth, personal projects without the time cap. Fits 1–3 low-traffic sites.
For developers, internal tools, client work, and small teams who need custom domains, better performance, and agent-side TLS.
Same capabilities as Basic with priority traffic, plus multiple agents on one tunnel for multi-location load balancing.
Need setup details or the upgrade path? Start with the Choose Your Path guide, Custom domains, and Security & TLS. Company, client, and team usage should be on a paid plan.
The product is intentionally simple at the start: anonymous and free registered tunnels help you get moving, while paid plans add the pieces that matter for professional use.
Run a tunnel from your terminal, use config files for multiple services, and avoid turning a simple localhost share into a dashboard-heavy workflow.
Free is for individual, non-commercial development. Paid plans are where custom domains, stronger privacy, and sustained professional use begin.
On paid plans, custom domains terminate TLS on the agent so payloads stay encrypted end-to-end. Assigned Cruma hostnames can also move to agent-side termination when certificates are ready.
Focused on developer tunnels, staging links, internal tools, and self-hosted services rather than a full enterprise edge platform. No policy engine. No ceremony.
Pick the track that matches what you're doing today. Move up whenever you want custom domains, multiple services, or a tighter setup.
Best for webhook testing, WIP demos, and quick localhost sharing without touching DNS or firewall rules.
Where Cruma becomes a paid workflow for professional developers, shared demos, internal tools, and client-facing staging.
For homelabs, isolated services, scripted tunnel management, and heavier daily use where Pro's priority traffic is useful.
Cruma is designed for developer tunnels, internal tools, homelabs, and shared staging — not a large enterprise policy platform. No complex policy engine, no formal SLA.
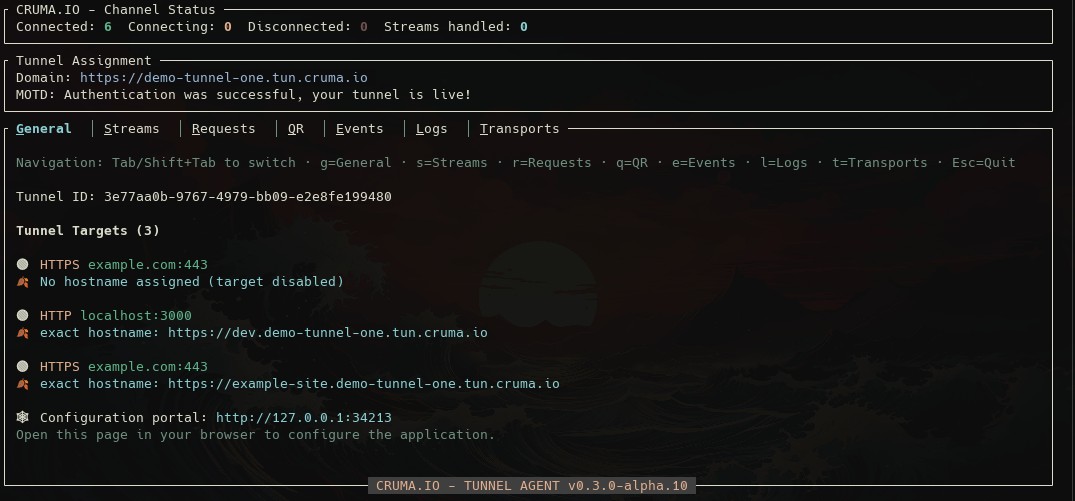
Two PoPs: EU-North (FI) and US-East. Agents keep HTTP/2 and QUIC channels open to the closest region with automatic reconnects on link failure.
Planned work now that Cruma is live and the core platform is in production.
Ship a Cruma Ingress/Gateway controller so cluster services get HTTPS endpoints exposed through cruma.io automatically.
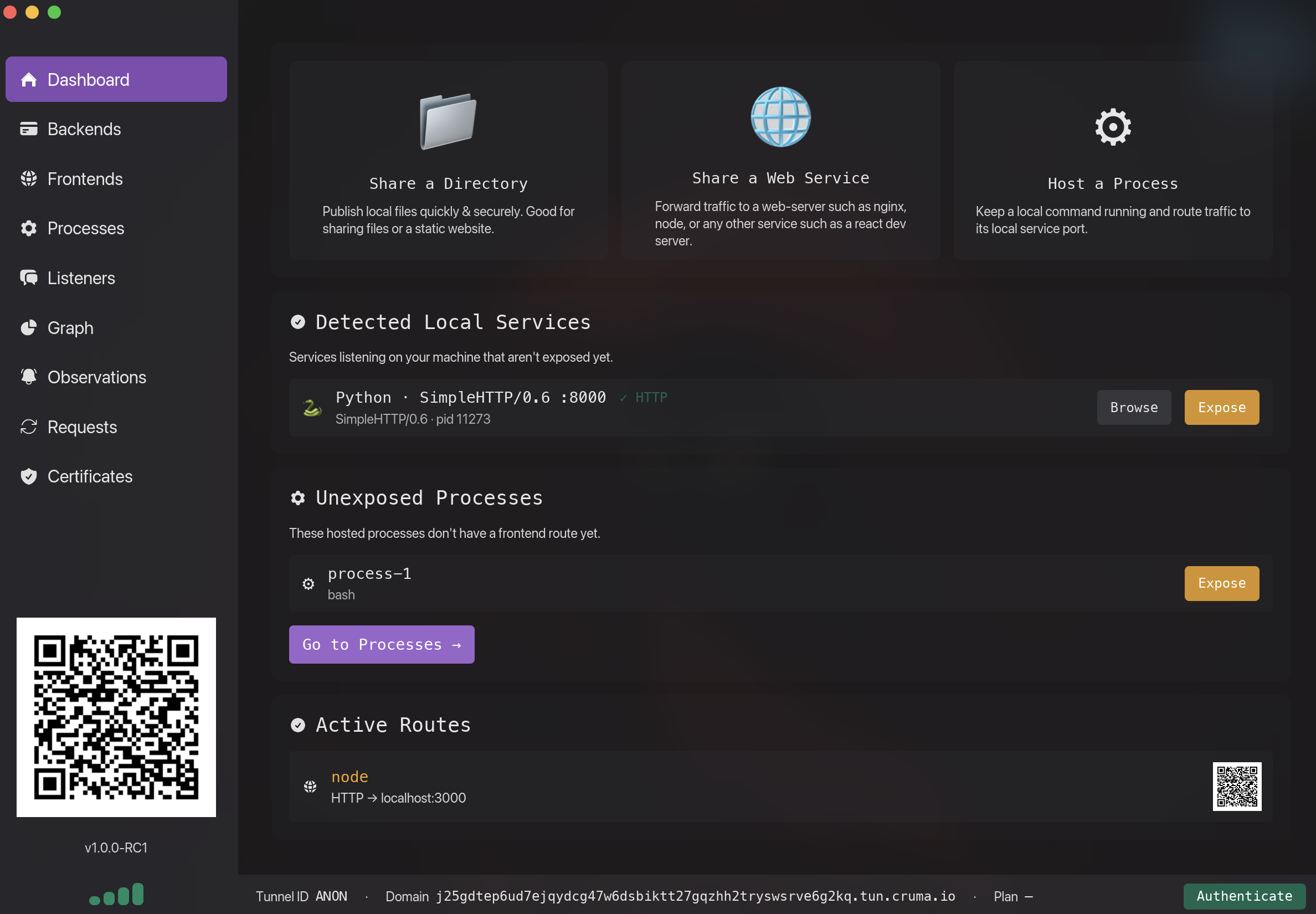
Configure and manage tunnels directly from your machine. We'll keep improving and adding features.
Native TCP & UDP tunnel support for game servers, custom protocols, and other non-HTTP workloads. Planning one or more public IPv6 addresses per tunnel.
Let applications create tunnels programmatically for ephemeral preview environments.
The latest tunnel agent is a single binary. Use our installer scripts or grab raw artifacts.

Or grab the raw binary: Download cruma.exe.
Prefer automation? Open PowerShell and run:
irm https://files.cruma.io/files/tunnel-agent/install/cruma.psm1 | iex ; Install-CrumaTunnelUninstall with:
irm https://files.cruma.io/files/tunnel-agent/install/cruma.psm1 | iex ; Uninstall-CrumaTunnelAlso available via WinGet and other package managers — in progress.
Download Cruma AppImage — the desktop GUI build for GNU/Linux.
Or install the terminal agent via the helper script:
curl -fsSL https://files.cruma.io/files/tunnel-agent/install/linux-install.sh | bashUninstall with the same script:
curl -fsSL https://files.cruma.io/files/tunnel-agent/install/linux-install.sh | bash -s -- --uninstallRaw binaries are also available here.
Debian, RPM, Arch, and Flatpak packaging flows are expanding in the release pipeline.
Direct download: Download Cruma.dmg.
Or install via Homebrew cask:
brew install --cask umbra-yurei/brew/crumaCruma.app and symlinks cruma into your PATH.brew upgrade --cask umbra-yurei/brew/cruma.Open Cruma.app from Applications or Spotlight to launch the menu bar app.
Cruma is a focused tunnel for developers, small teams, and homelabs. We optimize for fast setup, local-first tooling, and privacy options rather than enterprise policy suites. For anonymous tunnels Cruma terminates TLS at our edge; on subscribed plans TLS terminates on the agent (or your own proxy) for end-to-end encryption. Custom domains (CNAMEs) require a Basic or Pro subscription. High-level comparison with Cloudflare Tunnel and ngrok based on publicly documented features.
| Feature | Cruma | Cloudflare Tunnels | ngrok |
|---|---|---|---|
| Account-free quick tunnels | ✓ YesAnonymous mode for quick tunnels without an account. Aggressively rate-limited for fair usage. |
✓ YesSupported via "Quick Tunnels" at trycloudflare.com. Aggressively rate-limited; relaxed with a free account. |
× NoRequires an account and auth token. |
| Custom domains with E2E encryption | $ Yes (subscribed)Create a CNAME pointing to your tunnel's assigned domain. The agent terminates TLS locally and forwards to your app. Requires a paid subscription. |
× No (for E2E)Custom domains supported, but HTTP(S) terminates at Cloudflare's edge using Cloudflare-managed certs, so plaintext is visible at that point. |
$ PaidCustom domains on paid plans (see pricing). |
| Multi-endpoint | ✓ YesServe any number of endpoints using different hostnames. |
✓ YesServe any number of endpoints using different hostnames. |
$ PaidMultiple endpoints on paid plans only. |
| Protocol forwarding | ~ TCPTCP forwarding today; UDP is on the roadmap. |
✓ TCP & UDPcloudflared supports UDP forwarding (Warp/QUIC proxies require Zero Trust setup). |
~ TCPngrok's public service currently supports TCP forwarding. |
| Agent uplink protocols | ✓ QUIC + HTTP/2Agents maintain TLS-encrypted QUIC and HTTP/2 sessions for lower latency and better resilience. |
✓ QUIC + HTTP/2cloudflared can use QUIC uplinks and HTTP/2 over TLS in supported configs. |
~ HTTP/2ngrok speaks HTTP/2 to its control plane; no public QUIC uplink. |
| Local UX & tooling | ✓ TUI + desktop appDesktop app for configuration and request inspection, plus a terminal-based TUI. Headless mode available. |
~ CLI + hosted dashboardConfigured via CLI and Cloudflare's Zero Trust dashboards; no full-featured local web UI. |
~ CLI + remote inspectorRequest inspector and many config options live in the cloud dashboard. |
| HTTP request inspection | ✓ Local UIInspection in both the TUI and the desktop app; request logs never leave your machine. |
~ Zero Trust dashboardsRoutes through Cloudflare's edge so logs live in their SaaS; no local inspector. |
× Remote-onlyPrimary inspector UI runs in their cloud dashboard. |
| Serve local directories | ✓ Built-in directory serverServe a local directory directly from the agent — no nginx needed. |
× No built-in static serverRun your own web server or use Cloudflare Pages/Sites. |
× No built-in static serverRun a local server yourself and point ngrok at it. |
| Built-in access controls | ✓ IP allow-lists, forms & API keysAllow-list source IPs per tunnel (enforced at cruma.io), or put form-based auth or header API-key enforcement in front of any HTTP(S) backend. |
~ Via Zero Trust policiesHTTP access control via Cloudflare Access and Zero Trust, managed in their SaaS control plane. |
$ PaidAccess control and traffic-shaping on paid plans. |
| End-to-end encryption | ✓ Supported (subscribed)TLS terminates on the agent as soon as a certificate is generated (automatic), so Cruma's servers only see control-plane metadata and encrypted payloads. TLS passthrough also supported for CNAME/custom domains. |
× Not provider-blindFor standard HTTP(S) tunnels, TLS terminates at Cloudflare's edge, so plaintext is visible. Additional encryption to origin is possible, but Cloudflare remains in the trust chain. |
✓ SupportedTLS passthrough and agent-side TLS termination keep keys local. |
ngrok is closest to Cruma in tunnel and security capabilities. Cruma's differentiators are terminal-first tooling, simpler setup for non-specialists, and a pricing model that aims to stay affordable for individual developers and small teams.
Comparisons based on publicly documented capabilities as of Q1 2026. Spot an error? Email [email protected] and we'll update the table.
Anonymous tunnels need no signup. Paid plans start at $5/month.